Discovery questions
When joining a security position
or beginning to work for a client
Before beginning your actual work, you may want to acquire a general overview of the following fields :
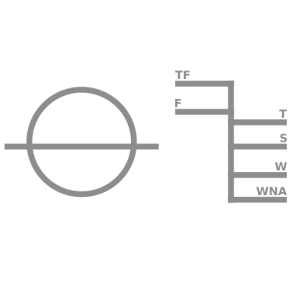
Threats <---> Security <---> Core activities
Having this in mind will help you to orientate your daily activities, and to take decisions when required.
Often, all this information can be found on intranets, shares, reports, etc. Nevertheless, IMHO, it is always better when one or several experienced colleague(s) explain these aspects, prioritizing and emphasizing. He or she will probably also be able to tell you the "off", all this informal knowledge which cannot be written.
1 - Core activities
1.1_ What is the purpose of the organisation ? What are its main activities ?
1.2_ What are the most sensitive processes & data ? What should be protected ?
1.3_ Are the most sensitive assets identified and listed somewhere ?
1.4_ Is there a reliable CMDB (up-to-date list of all assets & configurations) ? :)
1.5_ Where can I find a general schema of the IT infrastructure (ideally a functional one and a technical one) ?
1.6_ What is the IT strategy for the coming years ?
2 - Threats
2.1_ Are the main feared events / threats against the organisation identified ? (Reputational impact ? Data leakage ? Availability of critical services ? Financial loss ? List of core business processes ? Is there a top management guidance about these aspects ? etc.)
2.2_ Is there a list of adversaries, ranked according to their importance ? (Cybercrime, State-sponsored, Competitors, etc.)
2.3_ Is there a formalized list of "attack scenarios" ? (Based on threats, sensitive processes and IT infrastructure, try to guess what would be the most likely attack scenarios)
2.4_ Is there a list of significant security events / incidents ?
2.5_ Are there other organisations with which it is possible to share on security / threats ?
3 – Security
3.1_ What is the security organisation, detailed ?
3.2_ Is there a list of all IT security processes ? (In particular operational security, DFIR process, crisis meetings, etc.)
3.3_ Is there a list of all IT security components / products / services with a related view on "who does what" ?
3.4_ Where are the applicable security policies, and who could explain what is and isn’t applied ?
3.5_ Is it possible to consult reports of pentests run in the past ? Same question for on-site audit reports ? (for example at providers premises)
3.6_ Is there a formal risk acceptance process ? If yes, is there a list of risks already accepted ?
3.7_ What are unit’s relationships with : other IT teams, business units, audit, security teams of outsourcing companies, shareholders, subsidiaries, etc.
3.8_ How are exemptions to security rules managed ?
3.9_ Does the organisation have contractual possibilities for managing / controlling security issues with outsourcing partners ?
3.10_ Is there a list of VSP (Very Sensitive Persons) ? (like board members, assistants, secretaries, key business operations employees, sysadmins, dbas, etc.)
14 juillet 2017
Partager sur Twitter | Partager sur LinkedIn